extensible authentication protocol method smart card EAP ideally works on encrypted networks to transmit identifying information required for network authentication. Experts consider it a framework because it offers a range of authentication mechanisms for OTPs, token .
Unlock your iPhone and navigate to the home screen. Go to the “Settings” app, which is identified by the gear icon. Scroll down and tap on “NFC” from the list of available options. On the NFC screen, you will find a toggle .
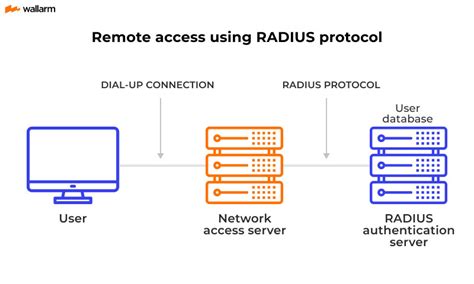
0 · radius authentication protocol
1 · network authentication protocol
2 · extensible authentication protocol windows 11
3 · extensible authentication protocol eap
4 · extensible authentication protocol
5 · eap method for authentication
6 · eap fast authentication protocol
7 · eap authentication protocol examples
To transfer your money faster than one to two business days, you have several .
radius authentication protocol
It supports various authentication methods, including as token cards, smart cards, certificates, one-time passwords and public key encryption. EAP methods protect a specific portal so that . The Extensible Authentication Protocol (EAP) supports a variety of authentication methods, each designed to meet specific security requirements and operational contexts. Among the most significant are EAP-TLS, EAP .
crypto contactless card singapore
Extensible Authentication Protocol (EAP) is a flexible framework supporting multiple authentication methods, such as passwords, smart cards, and digital certificates, primarily .EAP is an authentication framework, not a specific authentication mechanism. It provides some common functions and negotiation of authentication methods called EAP methods. There are currently about 40 different methods defined. Methods defined in IETF RFCs include EAP-MD5, EAP-POTP, EAP-GTC, EAP-TLS, EAP-IKEv2, EAP-SIM, EAP-AKA, and EAP-AKA'. Additionally, a number of vendor-specific methods and new proposals exist. Commonly used modern metho.The Extensible Authentication Protocol (EAP Protocol) is a wireless network that builds on the authentication method used by the Point-to-Point Protocol (PPP). This protocol is commonly used to connect a computer to the Internet.
EAP ideally works on encrypted networks to transmit identifying information required for network authentication. Experts consider it a framework because it offers a range of authentication mechanisms for OTPs, token .Extensible Authentication Protocol (EAP) is an authentication framework commonly used in wireless networks and other security architectures. It allows the use of different authentication methods and provides a standardized way .
These methods include token cards, Kerberos, One-Time Passwords (OTP), smart cards, Public Key Infrastructure (PKI), and more. The strength of EAP lies in its flexibility. It can support new .This article contains configuration information specific to the following authentication methods in EAP. EAP-Transport Layer Security (EAP-TLS): Standards-based EAP method that uses TLS .It supports various authentication methods, including as token cards, smart cards, certificates, one-time passwords and public key encryption. EAP methods protect a specific portal so that .
The Extensible Authentication Protocol (EAP) supports a variety of authentication methods, each designed to meet specific security requirements and operational contexts. .Extensible Authentication Protocol (EAP) is a flexible framework supporting multiple authentication methods, such as passwords, smart cards, and digital certificates, primarily .The Lightweight Extensible Authentication Protocol (LEAP) method was developed by Cisco Systems prior to the IEEE ratification of the 802.11i security standard. [3] Cisco distributed the .The Extensible Authentication Protocol (EAP Protocol) is a wireless network that builds on the authentication method used by the Point-to-Point Protocol (PPP). This protocol is commonly .
EAP ideally works on encrypted networks to transmit identifying information required for network authentication. Experts consider it a framework because it offers a range .Extensible Authentication Protocol (EAP) is an authentication framework commonly used in wireless networks and other security architectures. It allows the use of different authentication .These methods include token cards, Kerberos, One-Time Passwords (OTP), smart cards, Public Key Infrastructure (PKI), and more. The strength of EAP lies in its flexibility. It can support new .This flexibility enables EAP to support different authentication mechanisms, such as passwords, digital certificates, smart cards, token-based authentication, biometrics, and more. The EAP .
This article contains configuration information specific to the following authentication methods in EAP. EAP-Transport Layer Security (EAP-TLS): Standards-based EAP method that uses TLS .It supports various authentication methods, including as token cards, smart cards, certificates, one-time passwords and public key encryption. EAP methods protect a specific portal so that . The Extensible Authentication Protocol (EAP) supports a variety of authentication methods, each designed to meet specific security requirements and operational contexts. .
Extensible Authentication Protocol (EAP) is a flexible framework supporting multiple authentication methods, such as passwords, smart cards, and digital certificates, primarily .The Lightweight Extensible Authentication Protocol (LEAP) method was developed by Cisco Systems prior to the IEEE ratification of the 802.11i security standard. [3] Cisco distributed the .The Extensible Authentication Protocol (EAP Protocol) is a wireless network that builds on the authentication method used by the Point-to-Point Protocol (PPP). This protocol is commonly . EAP ideally works on encrypted networks to transmit identifying information required for network authentication. Experts consider it a framework because it offers a range .
Extensible Authentication Protocol (EAP) is an authentication framework commonly used in wireless networks and other security architectures. It allows the use of different authentication .These methods include token cards, Kerberos, One-Time Passwords (OTP), smart cards, Public Key Infrastructure (PKI), and more. The strength of EAP lies in its flexibility. It can support new .
network authentication protocol
extensible authentication protocol windows 11
cryptocurrency visa contactless card russia
extensible authentication protocol eap

Nintendo 3DS 2DS Official OEM NFC Reader/Writer Accessory For Amiibo CTR-012 1. JS .
extensible authentication protocol method smart card|network authentication protocol