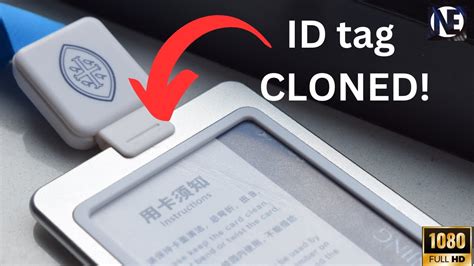
how-to-clone-mifare-classic-rfid-nfc-cards Here’s how you can clone Mifare NFC Classic 1K Cards using an Android smartphone with NFC capabilities. That’s right. You can use your cell phone to compromise the security of a company if they are using these types of cards. Auburn Sports Network game day coverage begins three hours prior to kickoff. Tiger Talk, Auburn's popular weekly radio show, returns on Thursday nights at 6 p.m. CT .
0 · rfid copy and paste
1 · nfc access card copy and paste
2 · how to copy rfid card
3 · how to copy nfc keys
4 · how to copy nfc cards
5 · how to copy nfc access cards
6 · copying rfid credentials
7 · copying rfid access cards
The NFL's wild card round of the playoffs will feature six games spread out over Jan. 13-15. All start times are in ET. Saturday, Jan. 13: AFC/NFC wild card matchup, 4:30 .

Chose your Mifare classic saved file. At thismpoint app only supports Mifare classic 1k with 4 byte UID. This will write UID and vendor info, with correct checksum. Checksum of UID is calculated by xor (exclusive OR of first byte of UID with next one and so on till the .I tried the exact thing some time ago, purchased a MIFARE card with writable sector 0 and tried cloning it with MIFARE classic tool. Did not work, I think it was due to the uni-card being . Chose your Mifare classic saved file. At thismpoint app only supports Mifare classic 1k with 4 byte UID. This will write UID and vendor info, with correct checksum. Checksum of UID is calculated by xor (exclusive OR of first byte of UID with next one and so on till the checksum byte. Here’s how you can clone Mifare NFC Classic 1K Cards using an Android smartphone with NFC capabilities. That’s right. You can use your cell phone to compromise the security of a company if they are using these types of cards.
I tried the exact thing some time ago, purchased a MIFARE card with writable sector 0 and tried cloning it with MIFARE classic tool. Did not work, I think it was due to the uni-card being encrypted. The MIFARE classic tool on the Play Store can't bruteforce cards if I remember correctly. So use the PM3 to retrieve key A and B of the needed sectors, and input them manually in MCT (or create and add a new key file) would be the easiest way to fully clone a Mifare Classic on a CUID gen2 card. The easiest way to clone Mifare NFC Classic 1K Cards is by using an Android smartphone with NFC capabilities. That’s right, your cellphone can be used to compromise the security of a company if they are using these types of cards (RFID security system). It is possible to clone with a magic card. But only a 4byte uid. Possible you need to install a fork (unleached, rogue master). I’m currently waiting to get the 7 byte uid clone possible. All my current cards have a 7 byte uid.
RFID/NFC Cloning Mifare Classic Smart Cards. The bash script i wrote can be found here: https://www.lostserver.com/static/nfc. The NFC Card reader/writer used for this POC is called.A quick demo video on how to break the encryption on a Mifare classic 1k card.
rfid copy and paste
If you want a clone of the card then you want both the UID and the data on the card to be copied across to the new card, but this isn’t normally possible due to the UID being read only. Enter the “UID changeable”, aka “Chinese backdoor” (seriously) cards, which allow you to change their UID. The goal here is to cover the process of cloning and editing RFID tags. MIFARE Classic ones especially, which are still widely used nowadays despite the many hacks found throughout the last few years. Chose your Mifare classic saved file. At thismpoint app only supports Mifare classic 1k with 4 byte UID. This will write UID and vendor info, with correct checksum. Checksum of UID is calculated by xor (exclusive OR of first byte of UID with next one and so on till the checksum byte. Here’s how you can clone Mifare NFC Classic 1K Cards using an Android smartphone with NFC capabilities. That’s right. You can use your cell phone to compromise the security of a company if they are using these types of cards.
I tried the exact thing some time ago, purchased a MIFARE card with writable sector 0 and tried cloning it with MIFARE classic tool. Did not work, I think it was due to the uni-card being encrypted. The MIFARE classic tool on the Play Store can't bruteforce cards if I remember correctly. So use the PM3 to retrieve key A and B of the needed sectors, and input them manually in MCT (or create and add a new key file) would be the easiest way to fully clone a Mifare Classic on a CUID gen2 card.
The easiest way to clone Mifare NFC Classic 1K Cards is by using an Android smartphone with NFC capabilities. That’s right, your cellphone can be used to compromise the security of a company if they are using these types of cards (RFID security system). It is possible to clone with a magic card. But only a 4byte uid. Possible you need to install a fork (unleached, rogue master). I’m currently waiting to get the 7 byte uid clone possible. All my current cards have a 7 byte uid. RFID/NFC Cloning Mifare Classic Smart Cards. The bash script i wrote can be found here: https://www.lostserver.com/static/nfc. The NFC Card reader/writer used for this POC is called.
A quick demo video on how to break the encryption on a Mifare classic 1k card. If you want a clone of the card then you want both the UID and the data on the card to be copied across to the new card, but this isn’t normally possible due to the UID being read only. Enter the “UID changeable”, aka “Chinese backdoor” (seriously) cards, which allow you to change their UID.
nfc access card copy and paste
how to copy rfid card
how to copy nfc keys
Listen live to Tide 100.9 online for free.Each network football broadcast spans seven hours from start to finish and includes the Tiger Tailgate Show, interviews with the head coach and exclusive post-game locker room .
how-to-clone-mifare-classic-rfid-nfc-cards|how to copy rfid card