rfid chip hacken This is just a short introduction into hacking of the Toniebox We gained a lot more knowledge about how the Toniebox works and what are the detailed processes . See more With 15 weeks of NFL games in the books, the 2021 NFL playoff picture is really starting to take shape. And the NFC, in particular, is playing host to a circus of a wild card .
0 · rfid scammers
1 · rfid scam
2 · rfid how to block
3 · rfid hack tool
4 · is rfid safe to hack
5 · how to stop rfid scanning
6 · how to prevent rfid cloning
7 · how to block rfid signal
Instead of “swiping” their plastic at the checkout counter, customers can “dip” their EMV cards into the chip reader. In most countries, authorizing the purchase requires a personal identification number (PIN) that only the user knows. This .
There are several different levels how to modify the Toniebox and the user’s experience without changing the hardware or the firmware. See moreThe PCB design of the Toniebox has a Debug Connector present. This arouses even more curiosity about going further down that rabbit hole. In this section I will . See moreThis is just a short introduction into hacking of the Toniebox We gained a lot more knowledge about how the Toniebox works and what are the detailed processes . See moreNFC Hacking using Arduino and RFID. This project demonstrates how to exploit vulnerabilities in NFC cards using Arduino and RFID technology. It provides a basic framework for reading and writing NFC cards using the MFRC522 RFID .
The NFC chips used within the Tonie figurine are keeping their information as a secret. They are locked into a so called „privacy mode“ that can only be disabled by using the password set by boxine.NFC Hacking using Arduino and RFID. This project demonstrates how to exploit vulnerabilities in NFC cards using Arduino and RFID technology. It provides a basic framework for reading and writing NFC cards using the MFRC522 RFID module.
RFID hackers have demonstrated how easy it is to get hold of information within RFID chips. As some chips are rewritable, hackers can even delete or replace RFID information with their own data. It's not too tricky for a hacker build his or . Learn how to prevent RFID hacking with our comprehensive guide. Increase your business safety and convenience while eliminating RFID attacks. Click here! MIFARE chips represent approximately 80% of the RFID passive tags in the world. Think of MIFARE as being the most used type of RFID tags. NFC is simply a newer technology to interact with the first two. With that little bit of knowledge, let’s focus on MIFARE. Keeping key cards in a reader proof wallet or case will help prevent skimming, where an attacker gets close enough with an NFC or RFID reader. Most importantly, physical penetration testing of security systems and practices will .
Practical guide to RFID hacking for penetration testers. Investigates the latest attack tools and techniques available for stealing and using RFID proximity badge information to gain unauthorized access to buildings and other secure areas. Chipkarten lieber im Anti-RFID-Portemonnaie aufbewahren? Wie man mit RFID -Chips Bastelspaß haben kann, das hat unser Netzbastler Moritz Metz schon in der letzten Netzbastel-Ausgabe gezeigt, in der er RFID-Podcastplayer baut. RFID is radio-based tech that can be exploited by hackers. Learn how to prevent RFID Hacking with seven security tips. To hack the chip, Nohl and Plotz reverse-engineered the cryptography on the MiFare chip through a painstaking process. They examined the actual MiFare Classic chip in exacting detail using.
The NFC chips used within the Tonie figurine are keeping their information as a secret. They are locked into a so called „privacy mode“ that can only be disabled by using the password set by boxine.
rfid scammers

rfid scam
NFC Hacking using Arduino and RFID. This project demonstrates how to exploit vulnerabilities in NFC cards using Arduino and RFID technology. It provides a basic framework for reading and writing NFC cards using the MFRC522 RFID module. RFID hackers have demonstrated how easy it is to get hold of information within RFID chips. As some chips are rewritable, hackers can even delete or replace RFID information with their own data. It's not too tricky for a hacker build his or .
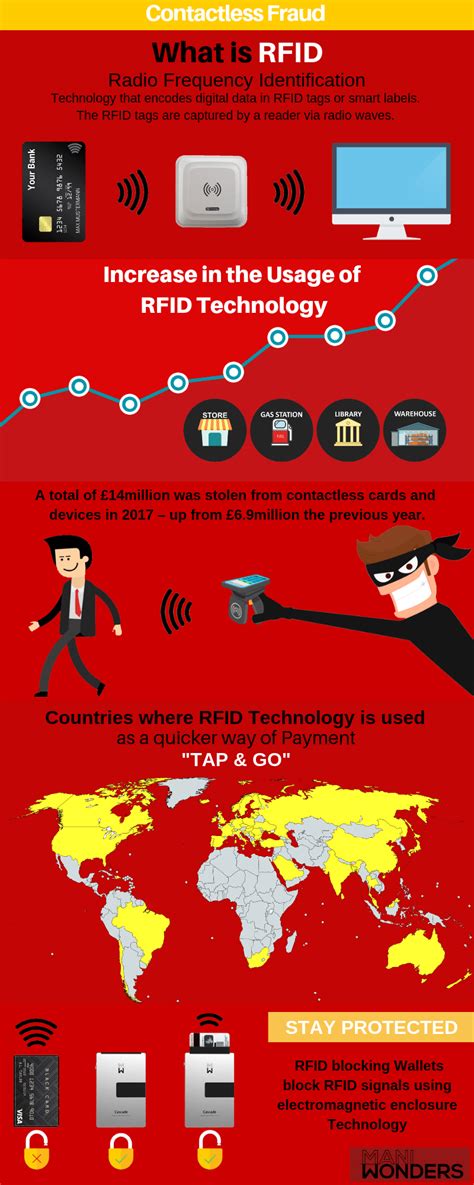
Learn how to prevent RFID hacking with our comprehensive guide. Increase your business safety and convenience while eliminating RFID attacks. Click here!
MIFARE chips represent approximately 80% of the RFID passive tags in the world. Think of MIFARE as being the most used type of RFID tags. NFC is simply a newer technology to interact with the first two. With that little bit of knowledge, let’s focus on MIFARE. Keeping key cards in a reader proof wallet or case will help prevent skimming, where an attacker gets close enough with an NFC or RFID reader. Most importantly, physical penetration testing of security systems and practices will .Practical guide to RFID hacking for penetration testers. Investigates the latest attack tools and techniques available for stealing and using RFID proximity badge information to gain unauthorized access to buildings and other secure areas.
Chipkarten lieber im Anti-RFID-Portemonnaie aufbewahren? Wie man mit RFID -Chips Bastelspaß haben kann, das hat unser Netzbastler Moritz Metz schon in der letzten Netzbastel-Ausgabe gezeigt, in der er RFID-Podcastplayer baut. RFID is radio-based tech that can be exploited by hackers. Learn how to prevent RFID Hacking with seven security tips.

rfid how to block

credit card to nfc ring
NFC stands for Near-field communication. See more
rfid chip hacken|how to stop rfid scanning