rfid tags security problems As you know that repudiation means when as user officially deny that he has done an action and we have no way to verify that whether he has performed that particular action. In the case of . See more The INY21 links to your AMS account, enabling safe access to all your Google .
0 · two types of rfid tags
1 · rfid tags and their uses
2 · rfid radio frequency identification tags
3 · rfid privacy and security issues
4 · retail anti theft security tags
5 · radio frequency identification tags are
6 · problems with rfid technology
7 · problems with rfid
This is our Tap Tag NFC tap-to-share keychain that you can customize to your own liking. A subscription-free and ready-to-setup digital profile is included on .Printed NFC Cards; Other NFC Tags. Blank NFC Key Fobs; Printed NFC Wristbands; UHF .
Like any other security devices and mechanism RFID is not flawless. Despite its widespread application and usage, RFID poses security threats and challenges that need to be addressed properly before deployment. This post aims to highlight several important RFID related security issues. Like any other . See moreRFID Counterfeiting: depending on the computing power, RFID can be classified into three categories: See moreIn a spoofing attack, the attacker masquerade as a legitimate user of the system. The attacker can pose himself as an authorized Object Naming Service user or database user. If an attacker can successfully get access to the system with his spoofed . See more
In this type of attack, an attacker tries to insert system commands to the RFID system instead of sending normal data.an example of RFID insert attack is that a tag carrying system . See more
As you know that repudiation means when as user officially deny that he has done an action and we have no way to verify that whether he has performed that particular action. In the case of . See more Poor physical security can result in tags being destroyed even if there is no specific gain for the attacker, leading to further risks associated with RFID technology.X-ray band or other radial band destroys data in tags, which an attacker can use to attack an RFID system-this type of attack is also known as radiation imprinting. Electromagnetic interference can disrupt communication between the tags and the reader.
Poor physical security can result in tags being destroyed even if there is no specific gain for the attacker, leading to further risks associated with RFID technology. The normal-tag approach achieves privacy protection by preventing the unauthorized reading of the output from the tag, blocking electric waves with aluminum foil or jamming waves to interfere with a tag’s ID being read by an adversary’s unauthenticated reader. Security issues The main security issue associated with the use of RFID systems is that they are susceptible to attacks or viruses from hackers and fraudsters. However, there is comfort in knowing that attacks on RFID systems aren’t easy to penetrate. Some people are concerned that attackers could use a handheld device in a crowd to read RFID information from nearby credit cards with contactless payment information embedded in them. Identity thieves could read the same information from an RFID-enabled passport or a security access card with an RFID chip.
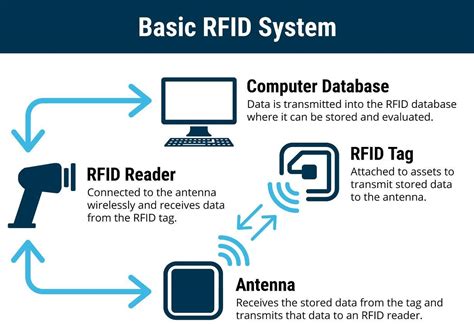
Specifically, Part II discusses how RFID technology works. Part III describes current and emerging uses of RFID technology, both in the private and public sectors. Part IV discusses the consumer privacy implications of RFID applications and database security issues.
two types of rfid tags

In this paper we analyze some of the most common types of attack on RFID tags: unauthorized disabling, unauthorized cloning, unauthorized tracking, and response replay. We introduce security mechanisms appropriate to defeat these attacks, and show how a recently proposed RFID authentication protocol uses them to achieve security. Examining the Security and Privacy Concerns of RFID: Part 1. R adio F requency Id entification, or RFID, is not a new technology. However, it is being used in new and different ways that have.
rfid chip einführung deutschland
Security issues in RFID system. The RFID scheme consists of several classes of tags and reader. These tags include an inadequate amount of memory and low-power capacity. However, there are numerous other issues in terms of . RFID tags are vulnerable to DoS/Desynchronization attacks because RFID tag and reader send out radio signals to each other in the open. Barcodes only reflect the beam of light received from the reader.X-ray band or other radial band destroys data in tags, which an attacker can use to attack an RFID system-this type of attack is also known as radiation imprinting. Electromagnetic interference can disrupt communication between the tags and the reader.
Poor physical security can result in tags being destroyed even if there is no specific gain for the attacker, leading to further risks associated with RFID technology. The normal-tag approach achieves privacy protection by preventing the unauthorized reading of the output from the tag, blocking electric waves with aluminum foil or jamming waves to interfere with a tag’s ID being read by an adversary’s unauthenticated reader. Security issues The main security issue associated with the use of RFID systems is that they are susceptible to attacks or viruses from hackers and fraudsters. However, there is comfort in knowing that attacks on RFID systems aren’t easy to penetrate.
rfid tags and their uses
Some people are concerned that attackers could use a handheld device in a crowd to read RFID information from nearby credit cards with contactless payment information embedded in them. Identity thieves could read the same information from an RFID-enabled passport or a security access card with an RFID chip.Specifically, Part II discusses how RFID technology works. Part III describes current and emerging uses of RFID technology, both in the private and public sectors. Part IV discusses the consumer privacy implications of RFID applications and database security issues.
In this paper we analyze some of the most common types of attack on RFID tags: unauthorized disabling, unauthorized cloning, unauthorized tracking, and response replay. We introduce security mechanisms appropriate to defeat these attacks, and show how a recently proposed RFID authentication protocol uses them to achieve security. Examining the Security and Privacy Concerns of RFID: Part 1. R adio F requency Id entification, or RFID, is not a new technology. However, it is being used in new and different ways that have.
Security issues in RFID system. The RFID scheme consists of several classes of tags and reader. These tags include an inadequate amount of memory and low-power capacity. However, there are numerous other issues in terms of .

rfid radio frequency identification tags

rfid casino chips bellagio
rfid chip for home use
The ST53G meets all relevant card-industry standards, including EMVCo™ compliance, ISO/IEC-14443 NFC card emulation, . ST is a global semiconductor leader delivering intelligent and energy-efficient products and .
rfid tags security problems|two types of rfid tags