how to rfid credit card hack Hackers using RFID scanners can theoretically steal money via your phone's tap-to-pay app. Here's how to prevent RFID hacking. An contactless NFC card, a free software app and its extensions. Nothing more. . NFC Crypto Hardware Wallet Your safety on autopilot. The app includes a complex library of functions that are activated via NFC. An administration .We’ve seen examples of the beautiful unique custom paint on NTAG215 cards or tokens, and .
0 · rfid scammers
1 · rfid scam
2 · rfid how to block
3 · rfid hack tool
4 · is rfid safe to hack
5 · how to stop rfid scanning
6 · how to prevent rfid cloning
7 · how to block rfid signal
We are a leading producer of Magnetic Cards in China which are ISO: 9001: .

The latest update is all about RFID and NFC, and how the Flipper Zero can interact with a variety of contactless protocols. Contactless tags are broadly separated into low . Learn how to prevent RFID hacking with our comprehensive guide. Increase your business safety and convenience while eliminating RFID attacks. Click here! The latest update is all about RFID and NFC, and how the Flipper Zero can interact with a variety of contactless protocols. Contactless tags are broadly separated into low . Learn how to prevent RFID hacking with our comprehensive guide. Increase your business safety and convenience while eliminating RFID attacks. Click here!
Hackers using RFID scanners can theoretically steal money via your phone's tap-to-pay app. Here's how to prevent RFID hacking.
Common RFID hacking techniques include RFID signal interception, tag cloning, replay attacks, brute-forcing cryptographic keys, signal jamming, and exploiting weak . [Aaron] is able to capture all the data from an RFID card, write that data to the SD card, and emulate a card using his RFID cloner.
Once a hacker has stolen your credit card data and other personally identifiable information, they can use it to do the following: Make unauthorized purchases. Create duplicate credit cards. .In this video, you’ll learn how to use your Arduino as an RFID cloner/reader where you’ll be able to clone a 13.56Mhz RFID tag/card and then use your new RFID tag to (open the garage . What can it do? The ChameleonMini can extract info from card keys and key fobs, including cloning the UID and storing the data for later. Card keys are the most obvious use, . To keep your RFID credit cards safe, keep your card in an RFID shield wallet or sleeve to block RFID scanners from reading your personal information. If you don’t have one .
rfid scammers
The goal here is to cover the process of cloning and editing RFID tags. MIFARE Classic ones especially, which are still widely used nowadays despite the many hacks found . The latest update is all about RFID and NFC, and how the Flipper Zero can interact with a variety of contactless protocols. Contactless tags are broadly separated into low . Learn how to prevent RFID hacking with our comprehensive guide. Increase your business safety and convenience while eliminating RFID attacks. Click here!
Hackers using RFID scanners can theoretically steal money via your phone's tap-to-pay app. Here's how to prevent RFID hacking. Common RFID hacking techniques include RFID signal interception, tag cloning, replay attacks, brute-forcing cryptographic keys, signal jamming, and exploiting weak . [Aaron] is able to capture all the data from an RFID card, write that data to the SD card, and emulate a card using his RFID cloner.Once a hacker has stolen your credit card data and other personally identifiable information, they can use it to do the following: Make unauthorized purchases. Create duplicate credit cards. .
In this video, you’ll learn how to use your Arduino as an RFID cloner/reader where you’ll be able to clone a 13.56Mhz RFID tag/card and then use your new RFID tag to (open the garage .
What can it do? The ChameleonMini can extract info from card keys and key fobs, including cloning the UID and storing the data for later. Card keys are the most obvious use, .
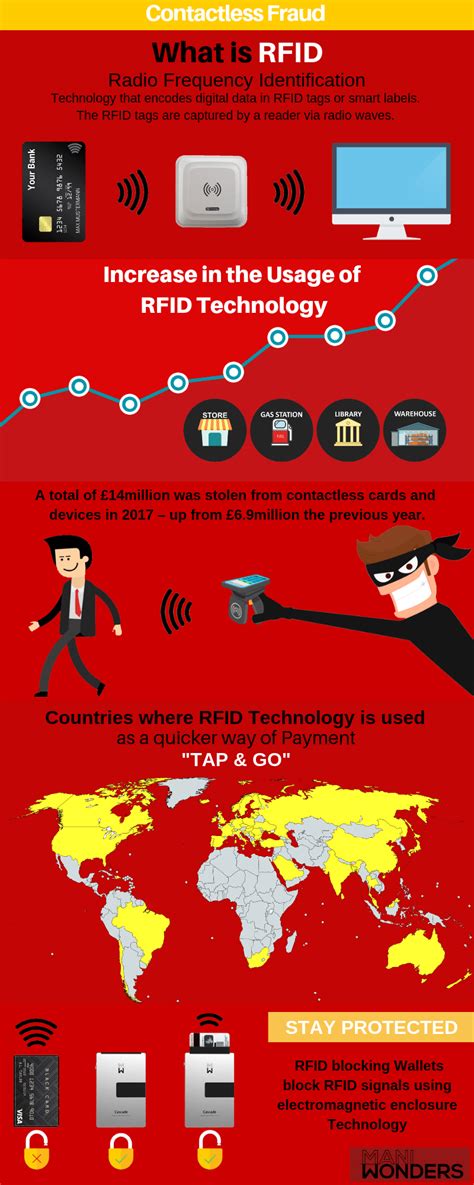
To keep your RFID credit cards safe, keep your card in an RFID shield wallet or sleeve to block RFID scanners from reading your personal information. If you don’t have one .
mifare cards protocol specification
mifare card copy
rfid scam
rfid how to block
The Bitcoin NFC card not only works seamlessly with NFC-enabled POS systems but also .
how to rfid credit card hack|rfid scam