rfid security tags A simple introduction to how RF and RFID tags are used in smart cards, toll . Yes, if your card does not have a contactless symbol on the back of the card, you can still make contactless purchases by loading your card into your digital wallet. You can then use the card with your smart phone or device to make contactless purchases.
0 · two types of rfid tags
1 · rfid tags and their uses
2 · rfid radio frequency identification tags
3 · rfid privacy and security issues
4 · retail anti theft security tags
5 · radio frequency identification tags are
6 · problems with rfid technology
7 · problems with rfid
8. Without getting too deep into the technology behind credit cards with RFID .
A simple introduction to how RF and RFID tags are used in smart cards, toll . RFID security tags are the simplest way for your business to keep track of inventory, shipments, and protect against theft. Small, inexpensive, and effective, if you don’t currently use them then you need to seriously reconsider! This article will explain what they are, how they work, and where they can be used.
A simple introduction to how RF and RFID tags are used in smart cards, toll collection, shop security, and other everyday applications. RFID tags come in three main types—passive, active, and semi-passive—each with distinct ranges, power sources, and use cases. RFID technology revolutionizes asset tracking and fixed inventory management by providing real-time .
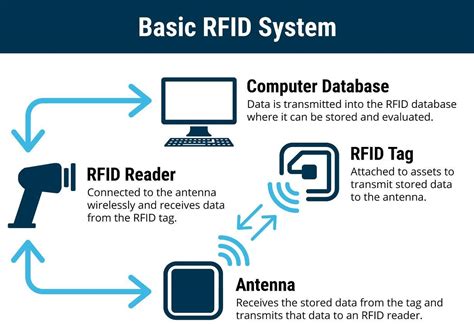
RF security tags are thus used to ensure specific products are safe from theft. Their activation also proves that an individual has stolen the item rather than bought it. This is because they are often turned off or removed by the checkout when they pass through a deactivation system. These items use wireless technology to function. A small chip -- known as an RFID tag -- is attached to or implanted in an object. The tags contain information that can be read at short range via radio waves. The chip and reader don't have to touch. Some RFID tags can be powered by a .
Enhanced security: RFID tags can be encrypted and programmed with unique identifiers, making it more difficult for counterfeit or unauthorized items to enter the supply chain. Real-time tracking: RFID tags can provide real-time data on the location and movement of items, allowing for better inventory management and supply chain optimization. An EAS tag is a hard plastic tag (or sometimes a label or sticker) that uses electronic article surveillance, or EAS, technology to alert store associates when an item has been stolen. Like an EAS security tag, an RFID tag is usually a .
RFID tags significantly improve long-haul logistics by offering real-time tracking, better asset management, and enhanced security. They allow companies to monitor the location of vehicles and shipments in transit, providing continuous updates .
RFID tag range refers to the maximum distance at which an RFID reader can effectively read the tag’s information. This range is influenced by several factors, including the type of tag, the power of the reader, and environmental conditions. Most RFID security tags are passive, but whether you opt for ultrahigh-frequency (UHF) tags, which are compliant with the EPC Gen 2 standard, or high-frequency (HF) tags, typically ISO-compliant, will depend on what’s critical to your value chain. RFID security tags are the simplest way for your business to keep track of inventory, shipments, and protect against theft. Small, inexpensive, and effective, if you don’t currently use them then you need to seriously reconsider! This article will explain what they are, how they work, and where they can be used. A simple introduction to how RF and RFID tags are used in smart cards, toll collection, shop security, and other everyday applications.
RFID tags come in three main types—passive, active, and semi-passive—each with distinct ranges, power sources, and use cases. RFID technology revolutionizes asset tracking and fixed inventory management by providing real-time .

can rfid readers read chip credit cards
two types of rfid tags

RF security tags are thus used to ensure specific products are safe from theft. Their activation also proves that an individual has stolen the item rather than bought it. This is because they are often turned off or removed by the checkout when they pass through a deactivation system. These items use wireless technology to function. A small chip -- known as an RFID tag -- is attached to or implanted in an object. The tags contain information that can be read at short range via radio waves. The chip and reader don't have to touch. Some RFID tags can be powered by a .
Enhanced security: RFID tags can be encrypted and programmed with unique identifiers, making it more difficult for counterfeit or unauthorized items to enter the supply chain. Real-time tracking: RFID tags can provide real-time data on the location and movement of items, allowing for better inventory management and supply chain optimization. An EAS tag is a hard plastic tag (or sometimes a label or sticker) that uses electronic article surveillance, or EAS, technology to alert store associates when an item has been stolen. Like an EAS security tag, an RFID tag is usually a . RFID tags significantly improve long-haul logistics by offering real-time tracking, better asset management, and enhanced security. They allow companies to monitor the location of vehicles and shipments in transit, providing continuous updates .
RFID tag range refers to the maximum distance at which an RFID reader can effectively read the tag’s information. This range is influenced by several factors, including the type of tag, the power of the reader, and environmental conditions.
rfid tags and their uses
can a wireless rfid reader read credit cards
Newer cards support newer algorithms for secure channel and card administration, but any card you buy is likely to have the same old test keys, with the same old SCP02 support, because .
rfid security tags|rfid radio frequency identification tags